In the previous posts we learnt about some attacks through which we can try to fool the victim so that he/she can log in to our fake page and be trapped and the other technique was a bit more easier but on that we can't able to retrieve the password we can only change that.
2. Facebook Hacking Through friends
Those tricks were good but using a remote keylogger is more easy.
How to Hack with a Remote Keylogger?
In this post we will discuss about the Ardamax Keylogger.
First of all the tools we required:
- Ardamax Keylogger
- Crypter
We need the above given tools. If you don't have then don't worry just download the files from the link given below
Now once you've downloaded the above given file, extract them to a particular folder. If you have an anti virus software on your system then disable your anti virus for a while or if you think that doing this is a bit risky for you then I recommend you to use a virtual machine.
Now on the folder you will find a setup file named Ardamax Keylogger, simply install that to the system as you install other applications.
Now follow the following steps to create your Remote Keylogger
Step 1: On the taskbar you'll see the icon of Ardamax keylogger, point on that and right click and then click on Enter Registration Key.
Enter the Registration name and Registration Key which you can find on the folder you downloaded before and click on ok.
Step 2: Go to the taskbar again and right click on the Ardamax keylogger icon and then click on the second option Remote install.
Now you'll see the welcome screen, simply click next now in the next window don't change anything the configuration should be same as the image given below.
Go Ahead, click on next now you'll see the email configuration window.
Dont' use hotmail account because hotmail does not allow keystroke logs to be mailed, I recommend you to use gmail. On the username type your gmail address and in password type your gmail password and leave the other things same as before don't change anything. Now click on next and go ahead.
You'll see the control window as shown below
Select the things you want to receive by this remote keylogger from your victim. Here I'm selecting only Keystrokes you can select all according to your wish. Again click on next and go ahead.
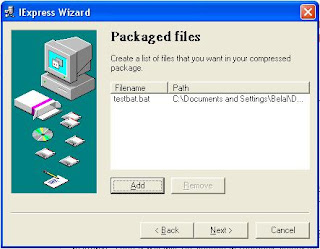
Now you'll see the Destination option Give an address to save your remote keylogger and click on Next. You can change the icon as well but that is not mandatory.
Now you're remote keylogger is created. After clicking next you'll see the Finish window with a dialogue box saying "Deployment package created successfully".
Now your remote keylogger is ready to use. Now you have to transfer this executable file to your victim's system and when your victim executes it he/she is now trapped.
Now the difficulties are:
1. You can not email an executable file.
2. Even if you somehow transferred or emailed this file to victim's system your victim will probably never execute a suspicious executable file.
3. Your remote keylogger can be easily detected by any Anti Virus application
So, first off all you need to crypt this executable file for avoiding anti virus detection. For cryption go to the folder which you have downloaded before. You'll see a folder named Crypter, open it and from that open the application named Simple Crypter-fud, you'll see a new window of the crypter.
Browse your remote keylogger and then click on Crypt. Your file is now crypted and will not be detected with an Anti Virus.
But,
Your remote keylogger is still an executable file and your victim will not gonna execute it on his/her system and you can't send an executable file with email.
So bind this .exe file with an .jpg image, when the victim will receive the email he/she will think that this is a simple jpg image, he will execute the jpg image and your remote keylogger will run silently in background and start doing his work.
You can bind it with a simple dos command. Just go to run, type cmd and hit enter. Command prompt will open. The syntax for binding file is
copy /b "filename.jpg" + "filename.exe" "outputname.jpg"
You need to type the file name with the complete address. I have kept both the files in my Local Disk (D:) so in my case the process will be
1. Open cmd
2. Change the directory to D: by typing D: and pressing enter
3. copy /b D:\ crypt.exe + belal.jpg atif.jpg
After this you will got the jpg file and your remote keylogger is hidden behind that jpg. When your victim will open the jpg image your remote keylogger will executes in background silently and start working. You'll get all the data of the keystrokes in your gmail account.
Disclaimer: The above provided tool is only for educational purpose. Don't use it to harm anyone or steal any confidential information. If you do that we will not responsible in any case.